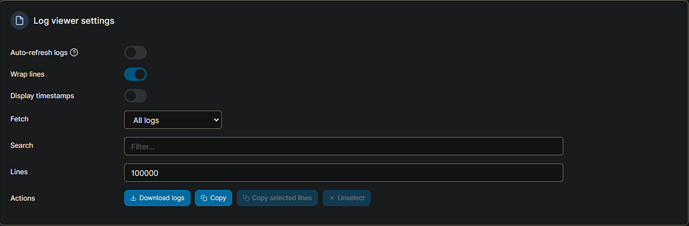
Here's what I get when using those log settings:
###############################################################
#@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@#
#@ @#
#@ ** WARNING ** WARNING ** WARNING ** WARNING ** @#
#@ @#
#@ YOU ARE RUNNING X11VNC WITHOUT A PASSWORD!! @#
#@ @#
#@ This means anyone with network access to this computer @#
#@ may be able to view and control your desktop. @#
#@ @#
#@ >>> If you did not mean to do this Press CTRL-C now!! <<< @#
#@ @#
#@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@#
_XSERVTransmkdir: ERROR: euid != 0,directory /tmp/.X11-unix will not be created.
[2024/08/01 11:23:26.130] Chrome Capture server listening on port 5589
#@ @#
#@ You can create an x11vnc password file by running: @#
#@ @#
#@ x11vnc -storepasswd password /path/to/passfile @#
#@ or x11vnc -storepasswd /path/to/passfile @#
#@ or x11vnc -storepasswd @#
#@ @#
#@ (the last one will use ~/.vnc/passwd) @#
#@ @#
#@ and then starting x11vnc via: @#
#@ @#
#@ x11vnc -rfbauth /path/to/passfile @#
#@ @#
#@ an existing ~/.vnc/passwd file from another VNC @#
#@ application will work fine too. @#
#@ @#
#@ You can also use the -passwdfile or -passwd options. @#
#@ (note -passwd is unsafe if local users are not trusted) @#
#@ @#
#@ Make sure any -rfbauth and -passwdfile password files @#
#@ cannot be read by untrusted users. @#
#@ @#
#@ Use x11vnc -usepw to automatically use your @#
#@ ~/.vnc/passwd or ~/.vnc/passwdfile password files. @#
#@ (and prompt you to create ~/.vnc/passwd if neither @#
#@ file exists.) Under -usepw, x11vnc will exit if it @#
#@ cannot find a password to use. @#
#@ @#
#@ @#
#@ Even with a password, the subsequent VNC traffic is @#
#@ sent in the clear. Consider tunnelling via ssh(1): @#
#@ @#
#@ http://www.karlrunge.com/x11vnc/#tunnelling @#
#@ @#
#@ Or using the x11vnc SSL options: -ssl and -stunnel @#
#@ @#
#@ Please Read the documentation for more info about @#
#@ passwords, security, and encryption. @#
#@ @#
#@ http://www.karlrunge.com/x11vnc/faq.html#faq-passwd @#
#@ @#
#@ To disable this warning use the -nopw option, or put @#
#@ 'nopw' on a line in your ~/.x11vncrc file. @#
#@ @#
#@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@#
###############################################################
01/08/2024 11:23:26 x11vnc version: 0.9.16 lastmod: 2019-01-05 pid: 9
01/08/2024 11:23:26 Using X display :99
01/08/2024 11:23:26 rootwin: 0x400 reswin: 0x200001 dpy: 0x5594d7f0
01/08/2024 11:23:26
01/08/2024 11:23:26 ------------------ USEFUL INFORMATION ------------------
01/08/2024 11:23:26 X DAMAGE available on display, using it for polling hints.
01/08/2024 11:23:26 To disable this behavior use: '-noxdamage'
01/08/2024 11:23:26
01/08/2024 11:23:26 Most compositing window managers like 'compiz' or 'beryl'
01/08/2024 11:23:26 cause X DAMAGE to fail, and so you may not see any screen
01/08/2024 11:23:26 updates via VNC. Either disable 'compiz' (recommended) or
01/08/2024 11:23:26 supply the x11vnc '-noxdamage' command line option.
01/08/2024 11:23:26
01/08/2024 11:23:26 Wireframing: -wireframe mode is in effect for window moves.
01/08/2024 11:23:26 If this yields undesired behavior (poor response, painting
01/08/2024 11:23:26 errors, etc) it may be disabled:
01/08/2024 11:23:26 - use '-nowf' to disable wireframing completely.
01/08/2024 11:23:26 - use '-nowcr' to disable the Copy Rectangle after the
01/08/2024 11:23:26 moved window is released in the new position.
01/08/2024 11:23:26 Also see the -help entry for tuning parameters.
01/08/2024 11:23:26 You can press 3 Alt_L's (Left "Alt" key) in a row to
01/08/2024 11:23:26 repaint the screen, also see the -fixscreen option for
01/08/2024 11:23:26 periodic repaints.
01/08/2024 11:23:26
01/08/2024 11:23:26 XFIXES available on display, resetting cursor mode
01/08/2024 11:23:26 to: '-cursor most'.
01/08/2024 11:23:26 to disable this behavior use: '-cursor arrow'
01/08/2024 11:23:26 or '-noxfixes'.
01/08/2024 11:23:26 using XFIXES for cursor drawing.
01/08/2024 11:23:26 GrabServer control via XTEST.
01/08/2024 11:23:26
01/08/2024 11:23:26 Scroll Detection: -scrollcopyrect mode is in effect to
01/08/2024 11:23:26 use RECORD extension to try to detect scrolling windows
01/08/2024 11:23:26 (induced by either user keystroke or mouse input).
01/08/2024 11:23:26 If this yields undesired behavior (poor response, painting
01/08/2024 11:23:26 errors, etc) it may be disabled via: '-noscr'
01/08/2024 11:23:26 Also see the -help entry for tuning parameters.
01/08/2024 11:23:26 You can press 3 Alt_L's (Left "Alt" key) in a row to
01/08/2024 11:23:26 repaint the screen, also see the -fixscreen option for
01/08/2024 11:23:26 periodic repaints.
01/08/2024 11:23:26
01/08/2024 11:23:26 XKEYBOARD: number of keysyms per keycode 7 is greater
01/08/2024 11:23:26 than 4 and 51 keysyms are mapped above 4.
01/08/2024 11:23:26 Automatically switching to -xkb mode.
01/08/2024 11:23:26 If this makes the key mapping worse you can
01/08/2024 11:23:26 disable it with the "-noxkb" option.
01/08/2024 11:23:26 Also, remember "-remap DEAD" for accenting characters.
01/08/2024 11:23:26
01/08/2024 11:23:26 X FBPM extension not supported.
Xlib: extension "DPMS" missing on display ":99".
01/08/2024 11:23:26 X display is not capable of DPMS.
01/08/2024 11:23:26 --------------------------------------------------------
01/08/2024 11:23:26
01/08/2024 11:23:26 Default visual ID: 0x21
01/08/2024 11:23:26 Read initial data from X display into framebuffer.
01/08/2024 11:23:26 initialize_screen: fb_depth/fb_bpp/fb_Bpl 16/16/3840
01/08/2024 11:23:26
01/08/2024 11:23:26 X display :99 is 16bpp depth=16 true color
01/08/2024 11:23:26
01/08/2024 11:23:26 Autoprobing TCP port
01/08/2024 11:23:26 Autoprobing selected TCP port 5900
01/08/2024 11:23:26 Autoprobing TCP6 port
01/08/2024 11:23:26 Autoprobing selected TCP6 port 5900
01/08/2024 11:23:26 listen6: bind: Address already in use
01/08/2024 11:23:26 Not listening on IPv6 interface.
01/08/2024 11:23:26
01/08/2024 11:23:26 Xinerama is present and active (e.g. multi-head).
01/08/2024 11:23:26 Xinerama: number of sub-screens: 1
01/08/2024 11:23:26 Xinerama: no blackouts needed (only one sub-screen)
01/08/2024 11:23:26
01/08/2024 11:23:26 fb read rate: 1546 MB/sec
01/08/2024 11:23:26 fast read: reset -wait ms to: 10
01/08/2024 11:23:26 fast read: reset -defer ms to: 10
01/08/2024 11:23:26 The X server says there are 10 mouse buttons.
01/08/2024 11:23:26 screen setup finished.
01/08/2024 11:23:26
01/08/2024 11:23:26 WARNING: You are running x11vnc WITHOUT a password. See
01/08/2024 11:23:26 WARNING: the warning message printed above for more info.
01/08/2024 11:23:26
The VNC desktop is: 4327c487ef12:0
0
******************************************************************************
Have you tried the x11vnc '-ncache' VNC client-side pixel caching feature yet?
The scheme stores pixel data offscreen on the VNC viewer side for faster
retrieval. It should work with any VNC viewer. Try it by running:
x11vnc -ncache 10 ...
One can also add -ncache_cr for smooth 'copyrect' window motion.
More info: http://www.karlrunge.com/x11vnc/faq.html#faq-client-caching
/home/chrome/node_modules/puppeteer-core/lib/cjs/puppeteer/node/ProductLauncher.js:153
throw new Errors_js_1.TimeoutError(error.message);
^
TimeoutError: Timed out after 30000 ms while waiting for the WS endpoint URL to appear in stdout!
at ChromeLauncher.launch (/home/chrome/node_modules/puppeteer-core/lib/cjs/puppeteer/node/ProductLauncher.js:153:23)
Node.js v18.16.0
(EE)
Fatal server error:
(EE) Server is already active for display 99
If this server is no longer running, remove /tmp/.X99-lock
and start again.
(EE)
###############################################################
#@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@#
#@ @#
#@ ** WARNING ** WARNING ** WARNING ** WARNING ** @#
#@ @#
#@ YOU ARE RUNNING X11VNC WITHOUT A PASSWORD!! @#
#@ @#
#@ This means anyone with network access to this computer @#
#@ may be able to view and control your desktop. @#
#@ @#
#@ >>> If you did not mean to do this Press CTRL-C now!! <<< @#
#@ @#
#@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@#
[2024/08/01 11:24:25.642] Chrome Capture server listening on port 5589
#@ @#
#@ You can create an x11vnc password file by running: @#
#@ @#
#@ x11vnc -storepasswd password /path/to/passfile @#
#@ or x11vnc -storepasswd /path/to/passfile @#
#@ or x11vnc -storepasswd @#
#@ @#
#@ (the last one will use ~/.vnc/passwd) @#
#@ @#
#@ and then starting x11vnc via: @#
#@ @#
#@ x11vnc -rfbauth /path/to/passfile @#
#@ @#
#@ an existing ~/.vnc/passwd file from another VNC @#
#@ application will work fine too. @#
#@ @#
#@ You can also use the -passwdfile or -passwd options. @#
#@ (note -passwd is unsafe if local users are not trusted) @#
#@ @#
#@ Make sure any -rfbauth and -passwdfile password files @#
#@ cannot be read by untrusted users. @#
#@ @#
#@ Use x11vnc -usepw to automatically use your @#
#@ ~/.vnc/passwd or ~/.vnc/passwdfile password files. @#
#@ (and prompt you to create ~/.vnc/passwd if neither @#
#@ file exists.) Under -usepw, x11vnc will exit if it @#
#@ cannot find a password to use. @#
#@ @#
#@ @#
#@ Even with a password, the subsequent VNC traffic is @#
#@ sent in the clear. Consider tunnelling via ssh(1): @#
#@ @#
#@ http://www.karlrunge.com/x11vnc/#tunnelling @#
#@ @#
#@ Or using the x11vnc SSL options: -ssl and -stunnel @#
#@ @#
#@ Please Read the documentation for more info about @#
#@ passwords, security, and encryption. @#
#@ @#
#@ http://www.karlrunge.com/x11vnc/faq.html#faq-passwd @#
#@ @#
#@ To disable this warning use the -nopw option, or put @#
#@ 'nopw' on a line in your ~/.x11vncrc file. @#
#@ @#
#@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@#
###############################################################
01/08/2024 11:24:25 x11vnc version: 0.9.16 lastmod: 2019-01-05 pid: 9
01/08/2024 11:24:25 XOpenDisplay(":99") failed.
01/08/2024 11:24:25 Trying again with XAUTHLOCALHOSTNAME=localhost ...
01/08/2024 11:24:25 ***************************************
01/08/2024 11:24:25 *** XOpenDisplay failed (:99)
*** x11vnc was unable to open the X DISPLAY: ":99", it cannot continue.
*** There may be "Xlib:" error messages above with details about the failure.
Some tips and guidelines:
** An X server (the one you wish to view) must be running before x11vnc is
started: x11vnc does not start the X server. (however, see the -create
option if that is what you really want).
** You must use -display <disp>, -OR- set and export your $DISPLAY
environment variable to refer to the display of the desired X server.
- Usually the display is simply ":0" (in fact x11vnc uses this if you forget
to specify it), but in some multi-user situations it could be ":1", ":2",
or even ":137". Ask your administrator or a guru if you are having
difficulty determining what your X DISPLAY is.
** Next, you need to have sufficient permissions (Xauthority)
to connect to the X DISPLAY. Here are some Tips:
- Often, you just need to run x11vnc as the user logged into the X session.
So make sure to be that user when you type x11vnc.
- Being root is usually not enough because the incorrect MIT-MAGIC-COOKIE
file may be accessed. The cookie file contains the secret key that
allows x11vnc to connect to the desired X DISPLAY.
- You can explicitly indicate which MIT-MAGIC-COOKIE file should be used
by the -auth option, e.g.:
x11vnc -auth /home/someuser/.Xauthority -display :0
x11vnc -auth /tmp/.gdmzndVlR -display :0
you must have read permission for the auth file.
See also '-auth guess' and '-findauth' discussed below.
** If NO ONE is logged into an X session yet, but there is a greeter login
program like "gdm", "kdm", "xdm", or "dtlogin" running, you will need
to find and use the raw display manager MIT-MAGIC-COOKIE file.
Some examples for various display managers:
gdm: -auth /var/gdm/:0.Xauth
-auth /var/lib/gdm/:0.Xauth
kdm: -auth /var/lib/kdm/A:0-crWk72
-auth /var/run/xauth/A:0-crWk72
xdm: -auth /var/lib/xdm/authdir/authfiles/A:0-XQvaJk
dtlogin: -auth /var/dt/A:0-UgaaXa
Sometimes the command "ps wwwwaux | grep auth" can reveal the file location.
Starting with x11vnc 0.9.9 you can have it try to guess by using:
-auth guess
(see also the x11vnc -findauth option.)
Only root will have read permission for the file, and so x11vnc must be run
as root (or copy it). The random characters in the filenames will of course
change and the directory the cookie file resides in is system dependent.
See also: http://www.karlrunge.com/x11vnc/faq.html
(EE)
Fatal server error:
(EE) Server is already active for display 99
If this server is no longer running, remove /tmp/.X99-lock
and start again.
(EE)
###############################################################
#@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@#
#@ @#
#@ ** WARNING ** WARNING ** WARNING ** WARNING ** @#
#@ @#
#@ YOU ARE RUNNING X11VNC WITHOUT A PASSWORD!! @#
#@ @#
#@ This means anyone with network access to this computer @#
#@ may be able to view and control your desktop. @#
#@ @#
#@ >>> If you did not mean to do this Press CTRL-C now!! <<< @#
#@ @#
#@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@#
#@ @#
#@ You can create an x11vnc password file by running: @#
#@ @#
#@ x11vnc -storepasswd password /path/to/passfile @#
#@ or x11vnc -storepasswd /path/to/passfile @#
#@ or x11vnc -storepasswd @#
#@ @#
#@ (the last one will use ~/.vnc/passwd) @#
#@ @#
#@ and then starting x11vnc via: @#
#@ @#
#@ x11vnc -rfbauth /path/to/passfile @#
#@ @#
#@ an existing ~/.vnc/passwd file from another VNC @#
#@ application will work fine too. @#
#@ @#
#@ You can also use the -passwdfile or -passwd options. @#
#@ (note -passwd is unsafe if local users are not trusted) @#
#@ @#
#@ Make sure any -rfbauth and -passwdfile password files @#
#@ cannot be read by untrusted users. @#
#@ @#
#@ Use x11vnc -usepw to automatically use your @#
#@ ~/.vnc/passwd or ~/.vnc/passwdfile password files. @#
#@ (and prompt you to create ~/.vnc/passwd if neither @#
#@ file exists.) Under -usepw, x11vnc will exit if it @#
#@ cannot find a password to use. @#
#@ @#
#@ @#
#@ Even with a password, the subsequent VNC traffic is @#
#@ sent in the clear. Consider tunnelling via ssh(1): @#
#@ @#
#@ http://www.karlrunge.com/x11vnc/#tunnelling @#
#@ @#
#@ Or using the x11vnc SSL options: -ssl and -stunnel @#
#@ @#
#@ Please Read the documentation for more info about @#
#@ passwords, security, and encryption. @#
#@ @#
#@ http://www.karlrunge.com/x11vnc/faq.html#faq-passwd @#
#@ @#
#@ To disable this warning use the -nopw option, or put @#
#@ 'nopw' on a line in your ~/.x11vncrc file. @#
#@ @#
#@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@#
###############################################################
01/08/2024 15:23:38 x11vnc version: 0.9.16 lastmod: 2019-01-05 pid: 9
01/08/2024 15:23:38 XOpenDisplay(":99") failed.
01/08/2024 15:23:38 Trying again with XAUTHLOCALHOSTNAME=localhost ...
01/08/2024 15:23:38 ***************************************
01/08/2024 15:23:38 *** XOpenDisplay failed (:99)
*** x11vnc was unable to open the X DISPLAY: ":99", it cannot continue.
*** There may be "Xlib:" error messages above with details about the failure.
Some tips and guidelines:
** An X server (the one you wish to view) must be running before x11vnc is
started: x11vnc does not start the X server. (however, see the -create
option if that is what you really want).
** You must use -display <disp>, -OR- set and export your $DISPLAY
environment variable to refer to the display of the desired X server.
- Usually the display is simply ":0" (in fact x11vnc uses this if you forget
to specify it), but in some multi-user situations it could be ":1", ":2",
or even ":137". Ask your administrator or a guru if you are having
difficulty determining what your X DISPLAY is.
** Next, you need to have sufficient permissions (Xauthority)
to connect to the X DISPLAY. Here are some Tips:
- Often, you just need to run x11vnc as the user logged into the X session.
So make sure to be that user when you type x11vnc.
- Being root is usually not enough because the incorrect MIT-MAGIC-COOKIE
file may be accessed. The cookie file contains the secret key that
allows x11vnc to connect to the desired X DISPLAY.
- You can explicitly indicate which MIT-MAGIC-COOKIE file should be used
by the -auth option, e.g.:
x11vnc -auth /home/someuser/.Xauthority -display :0
x11vnc -auth /tmp/.gdmzndVlR -display :0
you must have read permission for the auth file.
See also '-auth guess' and '-findauth' discussed below.
** If NO ONE is logged into an X session yet, but there is a greeter login
program like "gdm", "kdm", "xdm", or "dtlogin" running, you will need
to find and use the raw display manager MIT-MAGIC-COOKIE file.
Some examples for various display managers:
gdm: -auth /var/gdm/:0.Xauth
-auth /var/lib/gdm/:0.Xauth
kdm: -auth /var/lib/kdm/A:0-crWk72
-auth /var/run/xauth/A:0-crWk72
xdm: -auth /var/lib/xdm/authdir/authfiles/A:0-XQvaJk
dtlogin: -auth /var/dt/A:0-UgaaXa
Sometimes the command "ps wwwwaux | grep auth" can reveal the file location.
Starting with x11vnc 0.9.9 you can have it try to guess by using:
-auth guess
(see also the x11vnc -findauth option.)
Only root will have read permission for the file, and so x11vnc must be run
as root (or copy it). The random characters in the filenames will of course
change and the directory the cookie file resides in is system dependent.
See also: http://www.karlrunge.com/x11vnc/faq.html
[2024/08/01 15:23:39.294] Chrome Capture server listening on port 5589
/home/chrome/node_modules/@puppeteer/browsers/lib/cjs/launch.js:259
reject(new Error([
^
Error: Failed to launch the browser process! undefined
[20:42:0802/055212.844406:ERROR:bus.cc(399)] Failed to connect to the bus: Failed to connect to socket /run/dbus/system_bus_socket: No such file or directory
[20:20:0802/055212.887710:ERROR:ozone_platform_x11.cc(239)] Missing X server or $DISPLAY
[20:20:0802/055212.887738:ERROR:env.cc(255)] The platform failed to initialize. Exiting.
TROUBLESHOOTING: https://pptr.dev/troubleshooting
at ChildProcess.onClose (/home/chrome/node_modules/@puppeteer/browsers/lib/cjs/launch.js:259:24)
at ChildProcess.emit (node:events:525:35)
at ChildProcess._handle.onexit (node:internal/child_process:291:12)
Node.js v18.16.0
(EE)
Fatal server error:
(EE) Server is already active for display 99
If this server is no longer running, remove /tmp/.X99-lock
and start again.
(EE)
###############################################################
#@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@#
#@ @#
#@ ** WARNING ** WARNING ** WARNING ** WARNING ** @#
#@ @#
#@ YOU ARE RUNNING X11VNC WITHOUT A PASSWORD!! @#
#@ @#
#@ This means anyone with network access to this computer @#
#@ may be able to view and control your desktop. @#
#@ @#
#@ >>> If you did not mean to do this Press CTRL-C now!! <<< @#
#@ @#
#@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@#
[2024/08/02 05:52:13.904] Chrome Capture server listening on port 5589
#@ @#
#@ You can create an x11vnc password file by running: @#
#@ @#
#@ x11vnc -storepasswd password /path/to/passfile @#
#@ or x11vnc -storepasswd /path/to/passfile @#
#@ or x11vnc -storepasswd @#
#@ @#
#@ (the last one will use ~/.vnc/passwd) @#
#@ @#
#@ and then starting x11vnc via: @#
#@ @#
#@ x11vnc -rfbauth /path/to/passfile @#
#@ @#
#@ an existing ~/.vnc/passwd file from another VNC @#
#@ application will work fine too. @#
#@ @#
#@ You can also use the -passwdfile or -passwd options. @#
#@ (note -passwd is unsafe if local users are not trusted) @#
#@ @#
#@ Make sure any -rfbauth and -passwdfile password files @#
#@ cannot be read by untrusted users. @#
#@ @#
#@ Use x11vnc -usepw to automatically use your @#
#@ ~/.vnc/passwd or ~/.vnc/passwdfile password files. @#
#@ (and prompt you to create ~/.vnc/passwd if neither @#
#@ file exists.) Under -usepw, x11vnc will exit if it @#
#@ cannot find a password to use. @#
#@ @#
#@ @#
#@ Even with a password, the subsequent VNC traffic is @#
#@ sent in the clear. Consider tunnelling via ssh(1): @#
#@ @#
#@ http://www.karlrunge.com/x11vnc/#tunnelling @#
#@ @#
#@ Or using the x11vnc SSL options: -ssl and -stunnel @#
#@ @#
#@ Please Read the documentation for more info about @#
#@ passwords, security, and encryption. @#
#@ @#
#@ http://www.karlrunge.com/x11vnc/faq.html#faq-passwd @#
#@ @#
#@ To disable this warning use the -nopw option, or put @#
#@ 'nopw' on a line in your ~/.x11vncrc file. @#
#@ @#
#@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@#
###############################################################
02/08/2024 05:52:14 x11vnc version: 0.9.16 lastmod: 2019-01-05 pid: 9
02/08/2024 05:52:14 XOpenDisplay(":99") failed.
02/08/2024 05:52:14 Trying again with XAUTHLOCALHOSTNAME=localhost ...
02/08/2024 05:52:14 ***************************************
02/08/2024 05:52:14 *** XOpenDisplay failed (:99)
*** x11vnc was unable to open the X DISPLAY: ":99", it cannot continue.
*** There may be "Xlib:" error messages above with details about the failure.
Some tips and guidelines:
** An X server (the one you wish to view) must be running before x11vnc is
started: x11vnc does not start the X server. (however, see the -create
option if that is what you really want).
** You must use -display <disp>, -OR- set and export your $DISPLAY
environment variable to refer to the display of the desired X server.
- Usually the display is simply ":0" (in fact x11vnc uses this if you forget
to specify it), but in some multi-user situations it could be ":1", ":2",
or even ":137". Ask your administrator or a guru if you are having
difficulty determining what your X DISPLAY is.
** Next, you need to have sufficient permissions (Xauthority)
to connect to the X DISPLAY. Here are some Tips:
- Often, you just need to run x11vnc as the user logged into the X session.
So make sure to be that user when you type x11vnc.
- Being root is usually not enough because the incorrect MIT-MAGIC-COOKIE
file may be accessed. The cookie file contains the secret key that
allows x11vnc to connect to the desired X DISPLAY.
- You can explicitly indicate which MIT-MAGIC-COOKIE file should be used
by the -auth option, e.g.:
x11vnc -auth /home/someuser/.Xauthority -display :0
x11vnc -auth /tmp/.gdmzndVlR -display :0
you must have read permission for the auth file.
See also '-auth guess' and '-findauth' discussed below.
** If NO ONE is logged into an X session yet, but there is a greeter login
program like "gdm", "kdm", "xdm", or "dtlogin" running, you will need
to find and use the raw display manager MIT-MAGIC-COOKIE file.
Some examples for various display managers:
gdm: -auth /var/gdm/:0.Xauth
-auth /var/lib/gdm/:0.Xauth
kdm: -auth /var/lib/kdm/A:0-crWk72
-auth /var/run/xauth/A:0-crWk72
xdm: -auth /var/lib/xdm/authdir/authfiles/A:0-XQvaJk
dtlogin: -auth /var/dt/A:0-UgaaXa
Sometimes the command "ps wwwwaux | grep auth" can reveal the file location.
Starting with x11vnc 0.9.9 you can have it try to guess by using:
-auth guess
(see also the x11vnc -findauth option.)
Only root will have read permission for the file, and so x11vnc must be run
as root (or copy it). The random characters in the filenames will of course
change and the directory the cookie file resides in is system dependent.
See also: http://www.karlrunge.com/x11vnc/faq.html
/home/chrome/node_modules/@puppeteer/browsers/lib/cjs/launch.js:259
reject(new Error([
^
Error: Failed to launch the browser process! undefined
[20:42:0802/055217.080971:ERROR:bus.cc(399)] Failed to connect to the bus: Failed to connect to socket /run/dbus/system_bus_socket: No such file or directory
[20:20:0802/055217.103154:ERROR:ozone_platform_x11.cc(239)] Missing X server or $DISPLAY
[20:20:0802/055217.103168:ERROR:env.cc(255)] The platform failed to initialize. Exiting.
TROUBLESHOOTING: https://pptr.dev/troubleshooting
at ChildProcess.onClose (/home/chrome/node_modules/@puppeteer/browsers/lib/cjs/launch.js:259:24)
at ChildProcess.emit (node:events:525:35)
at ChildProcess._handle.onexit (node:internal/child_process:291:12)
Node.js v18.16.0
(EE)
Fatal server error:
(EE) Server is already active for display 99
If this server is no longer running, remove /tmp/.X99-lock
and start again.
(EE)
###############################################################
#@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@#
#@ @#
#@ ** WARNING ** WARNING ** WARNING ** WARNING ** @#
#@ @#
#@ YOU ARE RUNNING X11VNC WITHOUT A PASSWORD!! @#
#@ @#
#@ This means anyone with network access to this computer @#
#@ may be able to view and control your desktop. @#
#@ @#
#@ >>> If you did not mean to do this Press CTRL-C now!! <<< @#
#@ @#
#@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@#
[2024/08/02 05:52:18.195] Chrome Capture server listening on port 5589
#@ @#
#@ You can create an x11vnc password file by running: @#
#@ @#
#@ x11vnc -storepasswd password /path/to/passfile @#
#@ or x11vnc -storepasswd /path/to/passfile @#
#@ or x11vnc -storepasswd @#
#@ @#
#@ (the last one will use ~/.vnc/passwd) @#
#@ @#
#@ and then starting x11vnc via: @#
#@ @#
#@ x11vnc -rfbauth /path/to/passfile @#
#@ @#
#@ an existing ~/.vnc/passwd file from another VNC @#
#@ application will work fine too. @#
#@ @#
#@ You can also use the -passwdfile or -passwd options. @#
#@ (note -passwd is unsafe if local users are not trusted) @#
#@ @#
#@ Make sure any -rfbauth and -passwdfile password files @#
#@ cannot be read by untrusted users. @#
#@ @#
#@ Use x11vnc -usepw to automatically use your @#
#@ ~/.vnc/passwd or ~/.vnc/passwdfile password files. @#
#@ (and prompt you to create ~/.vnc/passwd if neither @#
#@ file exists.) Under -usepw, x11vnc will exit if it @#
#@ cannot find a password to use. @#
#@ @#
#@ @#
#@ Even with a password, the subsequent VNC traffic is @#
#@ sent in the clear. Consider tunnelling via ssh(1): @#
#@ @#
#@ http://www.karlrunge.com/x11vnc/#tunnelling @#
#@ @#
#@ Or using the x11vnc SSL options: -ssl and -stunnel @#
#@ @#
#@ Please Read the documentation for more info about @#
#@ passwords, security, and encryption. @#
#@ @#
#@ http://www.karlrunge.com/x11vnc/faq.html#faq-passwd @#
#@ @#
#@ To disable this warning use the -nopw option, or put @#
#@ 'nopw' on a line in your ~/.x11vncrc file. @#
#@ @#
#@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@#
###############################################################
02/08/2024 05:52:18 x11vnc version: 0.9.16 lastmod: 2019-01-05 pid: 9
02/08/2024 05:52:18 XOpenDisplay(":99") failed.
02/08/2024 05:52:18 Trying again with XAUTHLOCALHOSTNAME=localhost ...
02/08/2024 05:52:18 ***************************************
02/08/2024 05:52:18 *** XOpenDisplay failed (:99)
*** x11vnc was unable to open the X DISPLAY: ":99", it cannot continue.
*** There may be "Xlib:" error messages above with details about the failure.
Some tips and guidelines:
** An X server (the one you wish to view) must be running before x11vnc is
started: x11vnc does not start the X server. (however, see the -create
option if that is what you really want).
** You must use -display <disp>, -OR- set and export your $DISPLAY
environment variable to refer to the display of the desired X server.
- Usually the display is simply ":0" (in fact x11vnc uses this if you forget
to specify it), but in some multi-user situations it could be ":1", ":2",
or even ":137". Ask your administrator or a guru if you are having
difficulty determining what your X DISPLAY is.
** Next, you need to have sufficient permissions (Xauthority)
to connect to the X DISPLAY. Here are some Tips:
- Often, you just need to run x11vnc as the user logged into the X session.
So make sure to be that user when you type x11vnc.
- Being root is usually not enough because the incorrect MIT-MAGIC-COOKIE
file may be accessed. The cookie file contains the secret key that
allows x11vnc to connect to the desired X DISPLAY.
- You can explicitly indicate which MIT-MAGIC-COOKIE file should be used
by the -auth option, e.g.:
x11vnc -auth /home/someuser/.Xauthority -display :0
x11vnc -auth /tmp/.gdmzndVlR -display :0
you must have read permission for the auth file.
See also '-auth guess' and '-findauth' discussed below.
** If NO ONE is logged into an X session yet, but there is a greeter login
program like "gdm", "kdm", "xdm", or "dtlogin" running, you will need
to find and use the raw display manager MIT-MAGIC-COOKIE file.
Some examples for various display managers:
gdm: -auth /var/gdm/:0.Xauth
-auth /var/lib/gdm/:0.Xauth
kdm: -auth /var/lib/kdm/A:0-crWk72
-auth /var/run/xauth/A:0-crWk72
xdm: -auth /var/lib/xdm/authdir/authfiles/A:0-XQvaJk
dtlogin: -auth /var/dt/A:0-UgaaXa
Sometimes the command "ps wwwwaux | grep auth" can reveal the file location.
Starting with x11vnc 0.9.9 you can have it try to guess by using:
-auth guess
(see also the x11vnc -findauth option.)
Only root will have read permission for the file, and so x11vnc must be run
as root (or copy it). The random characters in the filenames will of course
change and the directory the cookie file resides in is system dependent.
See also: http://www.karlrunge.com/x11vnc/faq.html